
You can customize your WSS detection and management with features like:
- Web shell upload: detections, quarantine options, notifications, and reports
- Malicious URL management via Black, White, and Gray Lists
- Detection of personal information in files, documents, and databases
- Detection and recovery of changes in source files and web server configuration files
WSS Management Functions
System Safety Secured
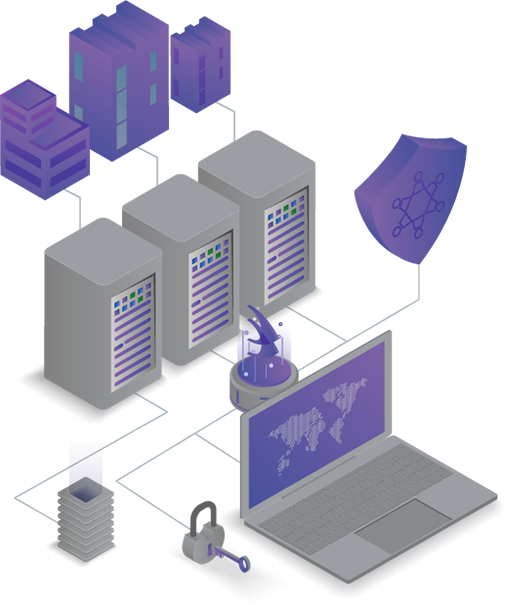
• Adjust system resource usage (CPU, memory)
• Redundancy support
• Attacker IP identification
Security Management Made Easy
• One-click auto-quarantines and reports
• Auto-detect target directories on setup and in operation
Limitless Compatibility
• Compatible with all OS (Windows, Linux, Unix)
Automate Detections & Updates
• Auto-update detection patterns
• Set up auto-backups of detection logs
• Filter website uploads with unauthorized extensions
Manage Hierarchy & Access
• Fully customize management and access rights
Full Integration
• Full support for external systems linking (SYSLOG, STMP, API, etc.)
• ESM, SIEM, configuration management, SMS, EMAIL, etc.
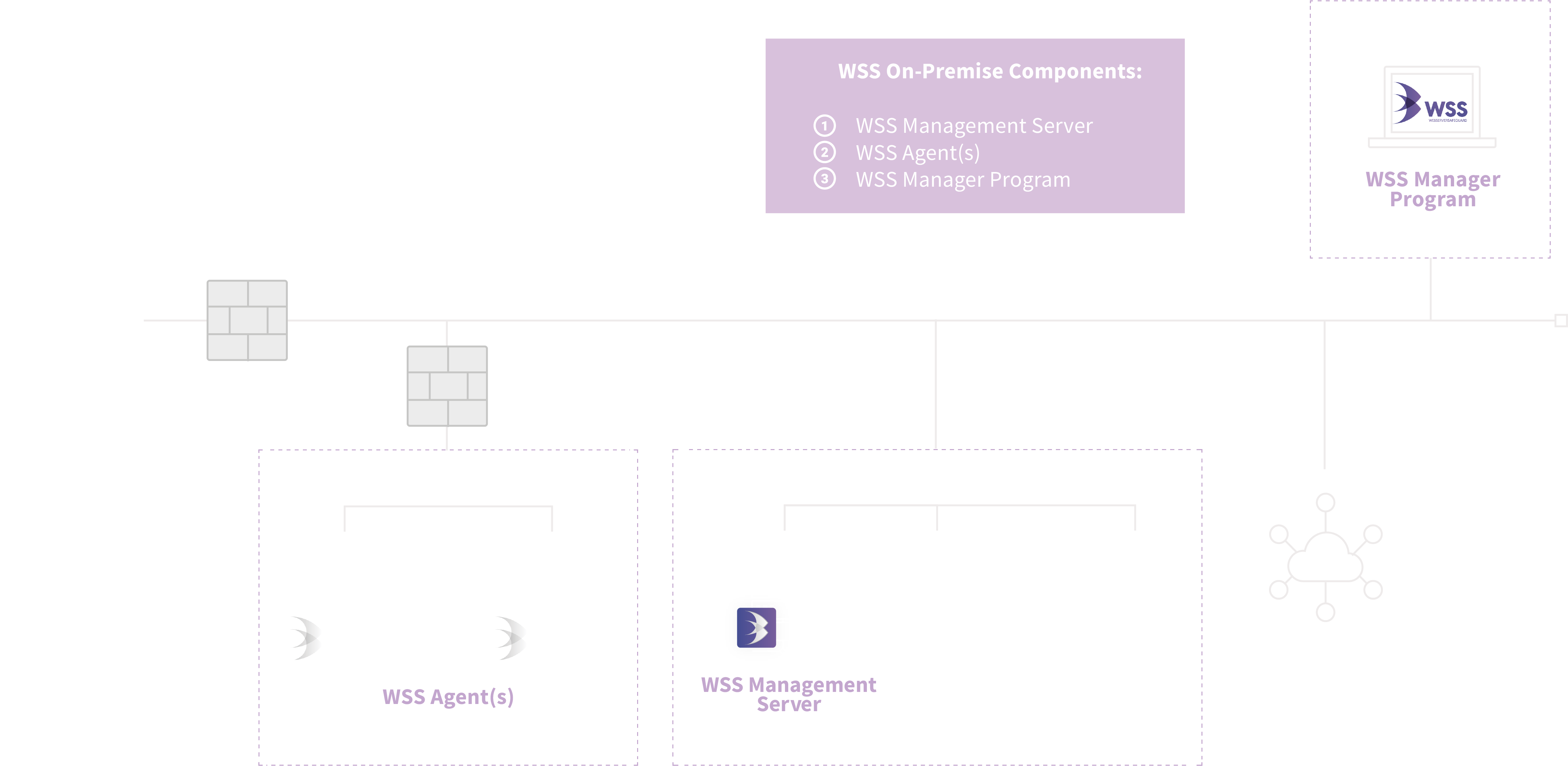
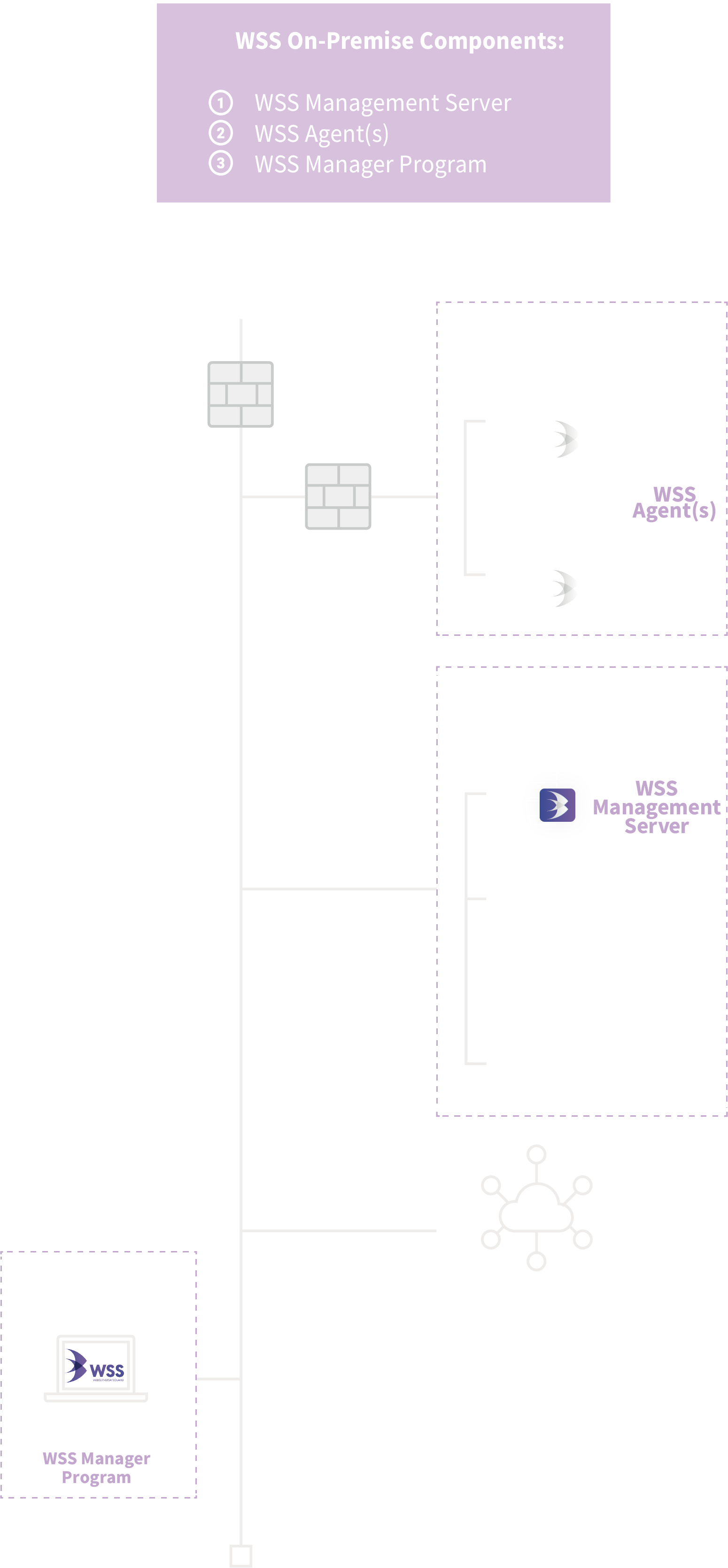
1. Management server
2. Agent
3. Manager (administrator) program
ONLINE SERVICES
WITH UMV